There has been a decent amount of press coming out of Microsoft recently, stemming from their April 5th “Windows Powers the Future of Hybrid Work” event that showcased a multitude of both Consumer- and Enterprise-focused feature updates and backend IT management tools updates.
One of the announced feature updates, in particular, Application Management for Edge, left me feeling like they’re essentially modernizing and building upon functionality that has in some aspects already been hiding in plain sight within Windows 10 (and now Windows 11 also) for several years.
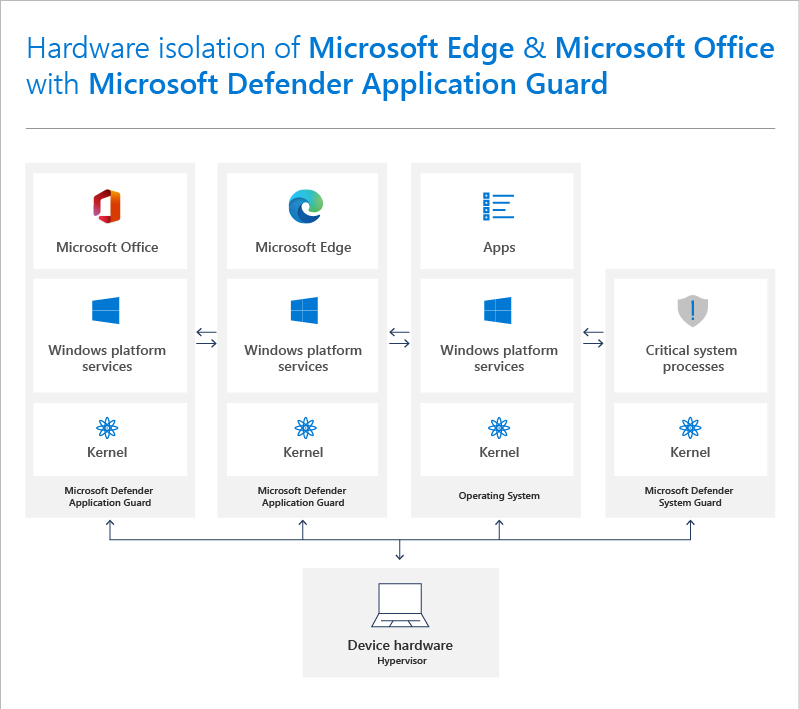
Going way back to 2016, a very useful security feature was added to the Microsoft Defender platform called Application Guard, which (admittedly somewhat confusingly, owing to the name) enables Enterprise orginzations to apply a Group Policy setting that triggered the function of enabling a Hyper-V-based container to be instantiated locally on each Windows endpoint whenever a user attempted to access an untrusted URL in Edge.
This served to locally containerize that browser application session on the device and essentially block the ability of a user to conduct certain actions such as copy/paste, printing, accessing unsanctioned or untrusted URLs, enabling the camera and mic, and several other browser-session-related functions.
Since the Edge browser application could be containerized in a virtualization layer locally on the endpoint itself, this served to extend the security hardening of the endpoint without solely relying on added security applications and services alone.
Containerization meant that it became extremely difficult for certain types of malicious attacks to become successful in exploiting the typical browser-based pathways they often utilized to get to the underlying Operating System for further attack proliferation.
More recently, the Application Guard functionality has been extended to now also allow the local Office/Microsoft 365 Apps for Enterprise clients themselves to be containerized through the same Hyper-V-based functionality that was originally applied to Edge, further extending the security of this tech to the other extremely common attack vector wherein users open a Word, Excel, or PowerPoint file that carries the risk of containing malicious macros or other exploits that then serve to proliferate as ransomware and other attack types.
Unfortunately, Windows’ built-in functions like Application Guard have flown under the radar for the most part in the years that it’s been available, despite the relative simplicity involved in configuring and applying it org-wide for any company that uses Win10/11 and has Microsoft 365 licensing.
Anecdotally, in Virteva’s experience working with hundreds of organizations in the past few years, a significant majority of them had never heard of Application Guard before until we brought it up, let alone have it actively deployed via Group Policy within their environment.
This has left many organizations dependent on traditional antivirus software, which has typically been ineffective in protecting organizations from cyberattacks.
Thankfully, the ease of deployment and relatively low administrative overhead that is exhibited by leveraging Application Guard have led many to take our advice and activate it.
There are certainly added benefits coming with Application Management for Edge when it releases, most likely later this year. We’re eager to get our hands on it to start testing it and working out where it overlaps with Application Guard’s functionality and where it goes beyond.
In the meantime, we’d certainly advise all Microsoft 365-licensed organizations to give Application Guard a serious look and engage Virteva to obtain our help in effectively configuring and applying it as part of a broader security strategy and attack surface reduction practice that we help many organizations with every day.
Supplementary image from: https://docs.microsoft.com/en-us/windows/security/threat-protection/microsoft-defender-application-guard/md-app-guard-overview