Financial institutions face unique technology challenges that directly threaten their operations, customer trust, and regulatory standing. Banks, investment firms, insurance companies, and other financial organizations depend on complex IT systems processing millions of transactions daily, storing vast amounts of sensitive customer data, and connecting to countless third-party services.
A single system failure, data breach, or cyberattack can result in massive financial losses, regulatory penalties, and irreparable damage to reputation. IT risk management in financial services isn’t just about protecting technology—it’s about safeguarding the institution’s ability to serve customers, maintain regulatory compliance, and preserve the trust that forms the foundation of all financial relationships.
The Growing Impact of Technology Risk on Financial Stability
Technology has become so deeply embedded in financial services that IT risks now represent systemic threats to institutional stability and broader financial markets.
How Cyber Incidents Threaten Financial Operations
Cyberattacks targeting financial institutions have grown both more frequent and more sophisticated. Ransomware can lock critical banking systems, preventing transaction processing and customer access. Data breaches expose sensitive customer financial information, triggering regulatory penalties and class-action lawsuits.
The interconnected nature of financial systems means attacks on one institution can cascade through entire networks, amplifying the importance of IT risk management across the entire financial sector.
System Failures and Third-Party Dependencies
Beyond intentional attacks, accidental system failures create significant risks. Software bugs, hardware failures, or misconfigurations can crash critical systems. In financial services where uptime expectations approach 100%, even brief outages damage customer relationships.
Third-party technology dependencies add complexity—financial institutions rely on cloud providers, payment processors, and countless technology partners. Each represents a potential point of failure requiring attention in comprehensive IT and risk management strategies.
Key Types of IT Risks Facing Financial Institutions
Understanding specific risk categories helps prioritize protective measures and allocate resources effectively.
Cybersecurity and Data Protection Risks
Financial institutions represent prime targets for cybercriminals due to direct access to money and valuable customer data. Key threats include external attacks from organized crime, insider threats from employees, social engineering targeting staff, malware and ransomware infections, and data breaches exposing customer information. Regulatory requirements mandate strict data protection, making breaches particularly costly.
Operational and System Availability Risks
Core banking systems, trading platforms, and payment processors must operate reliably. Operational risks include hardware failures, software bugs causing transaction errors, capacity limitations during peak usage, failed updates, and network outages disrupting connectivity. Even brief unavailability triggers regulatory scrutiny and damages the competitive position.
Third-Party and Vendor Technology Risks
Financial institutions depend on numerous technology vendors. Third-party risks include vendor security breaches exposing institution data, service disruptions at critical vendors, inadequate vendor security practices, and a lack of visibility into vendor security posture. Effective IT risk management requires rigorous vendor assessment and ongoing monitoring.
Core Strategies for Effective IT Risk Management
Financial institutions need comprehensive approaches addressing the full spectrum of technology risks.
Establishing a Strong IT Risk Governance Framework
Governance provides the foundation for effective IT risk management. This framework defines roles, responsibilities, policies, and processes governing how technology risks are identified, assessed, mitigated, and monitored.
Board-level oversight ensures technology risk receives appropriate senior attention. Clear accountability structures assign specific risk management responsibilities to Chief Information Security Officers, Chief Technology Officers, and Chief Risk Officers with appropriate authority and resources.
Risk appetite statements articulate how much technology risk the institution is willing to accept in pursuit of business objectives. These statements guide decision-making about technology investments, security controls, and risk mitigation strategies.
Integrating IT Security Risk Management Into Daily Operations
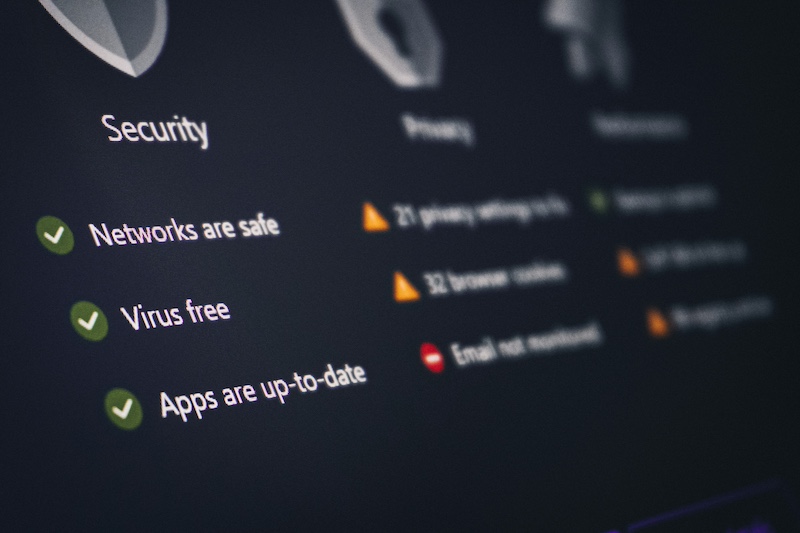
IT security risk management must be woven throughout daily operations rather than existing as a separate compliance function. Security-by-design principles build protection into systems from the beginning rather than adding security as an afterthought. DevSecOps practices integrate security throughout the software development lifecycle, with automated security testing catching issues early when they’re easiest to fix.
Conducting Regular Risk Assessments and Audits
Regular assessment identifies new risks, evaluates changing threat landscapes, and measures control effectiveness. Annual comprehensive risk assessments provide a broad overview of institutional risk posture, while more frequent targeted assessments focus on high-risk areas. Penetration testing simulates real-world attacks, revealing vulnerabilities that theoretical assessments might miss.
Using IT Risk Management Software to Improve Visibility and Control
Technology platforms enhance IT risk management effectiveness by providing centralized visibility, automated processes, and comprehensive reporting.
Key Capabilities of IT Risk Management Software
Modern platforms provide several important capabilities:
- Centralized risk registers documenting all identified risks, their assessments, mitigation strategies, and ownership
- Automated risk assessments streamlining evaluation processes and ensuring consistency
- Real-time monitoring,g tracking risk indicators, rs and control effectiveness are continuously
- Compliance management mapping controls to regulatory requirements and tracking compliance status
- Vendor risk management, assessing and monitoring third-party risks systematically
- Reporting and dashboards providing executives with visibility into risk posture and trends
Benefits of Centralized Risk Management Platforms
Centralized platforms replace fragmented spreadsheets and disconnected tools with unified systems providing comprehensive visibility. This consolidation improves accuracy, reduces duplication, and ensures consistent risk assessment methodologies across the organization.
Integration with other systems—security tools, audit platforms, compliance management—creates cohesive risk ecosystems where information flows automatically between systems. This integration reduces manual work while improving data quality and timeliness.

Managing IT Risk Across Complex Financial Environments
Modern financial institutions operate in complex, distributed environments requiring sophisticated risk management approaches.
Balancing Innovation and Risk in Digital Transformation
Financial institutions pursuing digital transformation—cloud migration, mobile banking, AI-powered services—must balance innovation against risk. Overly cautious approaches to IT risk management stifle innovation and competitive advantage. Excessively aggressive innovation without adequate risk consideration creates dangerous exposures.
Effective strategies enable innovation within acceptable risk boundaries. Sandbox environments allow experimentation with new technologies in controlled settings. Incremental rollouts limit exposure during initial deployments. Comprehensive testing validates security and reliability before full implementation.
Aligning IT Risk Management With Regulatory Expectations
Financial regulators worldwide have increased focus on technology risk. Requirements vary by jurisdiction and institution type, but common themes include board-level oversight, comprehensive risk assessment, incident response capabilities, business continuity planning, and third-party risk management.
Regulatory examinations specifically assess IT risk management maturity. Institutions must demonstrate not just policies on paper but evidence of effective implementation. Documentation proving regular risk assessments, control testing, incident response exercises, and continuous improvement becomes necessary for regulatory compliance.
Forward-thinking institutions view regulatory requirements as minimum baselines rather than ultimate goals. Leading practices exceed regulatory minimums, recognizing that adequate IT risk management protects not just against regulatory penalties but against far more costly operational disruptions and security incidents.
Conclusion
Effective IT risk management has become foundational to financial institution stability and success. Technology risks—from cyberattacks and system failures to third-party vulnerabilities—threaten operations, compliance, and customer trust in ways that can quickly become existential.
Financial institutions must implement comprehensive IT risk management strategies encompassing strong governance, integrated security risk management, regular assessments, appropriate technology platforms, and a careful balance between innovation and risk. IT risk management software provides necessary visibility and control over complex risk environments while enabling efficient processes and comprehensive reporting.